How to Create a Team Signature Governance Policy That People Will Actually Follow
A practical governance policy for defining ownership, locked fields, approval flow, and review rhythm without adding unnecessary bureaucracy.

Email signature work is often treated like a finishing touch, but without governance, signatures gradually drift into a patchwork of old branding, unsupported layouts, and legal text that nobody can confidently verify. When operations, brand, and compliance owners approach creating a team signature governance policy as a business system rather than a cosmetic task, they reduce rework, shorten onboarding, and protect every outgoing message from looking improvised. That shift matters because recipients notice small inconsistencies immediately: a cropped logo suggests poor coordination, a broken phone link slows down replies, and an outdated disclaimer creates avoidable risk. A strong signature program turns those weak points into a steady layer of trust that supports sales conversations, customer support, recruiting, and executive communication at the same time.
This guide is built around a practical idea: a lightweight policy that keeps signatures consistent without turning every change into a slow committee process. Instead of chasing design tricks or copying whatever another company pasted into Gmail, the better route is to define a repeatable operating model, confirm which fields truly matter, test on the email clients your team already uses, and create a light governance rhythm that keeps everything current. That is the purpose of a lightweight governance policy: a way to connect branding, usability, compliance, and execution so the signature stays useful after launch rather than looking good for one week and then drifting out of control.
Define where control is necessary and where flexibility is safe
The first conversation should not be about fonts, banners, or icon styles. It should be about the operational promise behind the signature. Policy is useful only when it is tied to everyday behavior, so the first job is to define where the company needs control and where it can safely allow limited flexibility. That means identifying who owns the master template, which teams need a variation, which fields can be personalized, and where the signature should actively help a conversation move forward. When those questions are skipped, people compensate by making local edits, and local edits are usually the fastest path to visual drift. Starting with governance sounds less exciting than starting with design, but it is exactly what allows the design to remain consistent after the first rollout.
Requirement gathering works best when it is specific and slightly uncomfortable. That usually means separating identity fields from structural or regulated content, then making approval paths clear enough that nobody needs to guess. Ask stakeholders to point out the information recipients actually use, the elements that regularly become outdated, and the details that should never be touched without approval. That conversation usually reveals hidden complexity: regional phone formats, temporary campaign links, recruitment banners, holiday schedules, or legal clauses that vary by market. Once those realities are documented, the signature stops being an abstract brand asset and becomes a manageable operational product with clear constraints.
- Writing a policy that describes ideals but does not connect to the actual publishing workflow.
- Leaving approvals vague so urgent edits turn into informal back-channel decisions.
- Allowing too many undocumented exceptions until the policy no longer reflects reality.
Turn governance rules into visible structure
A reliable signature layout is less about decoration and more about disciplined hierarchy. The layout must reflect those rules by making locked areas stable and editable areas obvious, otherwise people will work around the policy instead of with it. The strongest versions make the name easy to find, the role easy to understand, and the primary action easy to scan without forcing the recipient to interpret a crowded block of links. Visual restraint is useful because the email body already carries the main message; the signature should support credibility and provide a small next step, not compete with the content above it. Teams that respect hierarchy usually end up with signatures that travel better across Gmail, Outlook, Apple Mail, forwarding chains, and mobile replies.
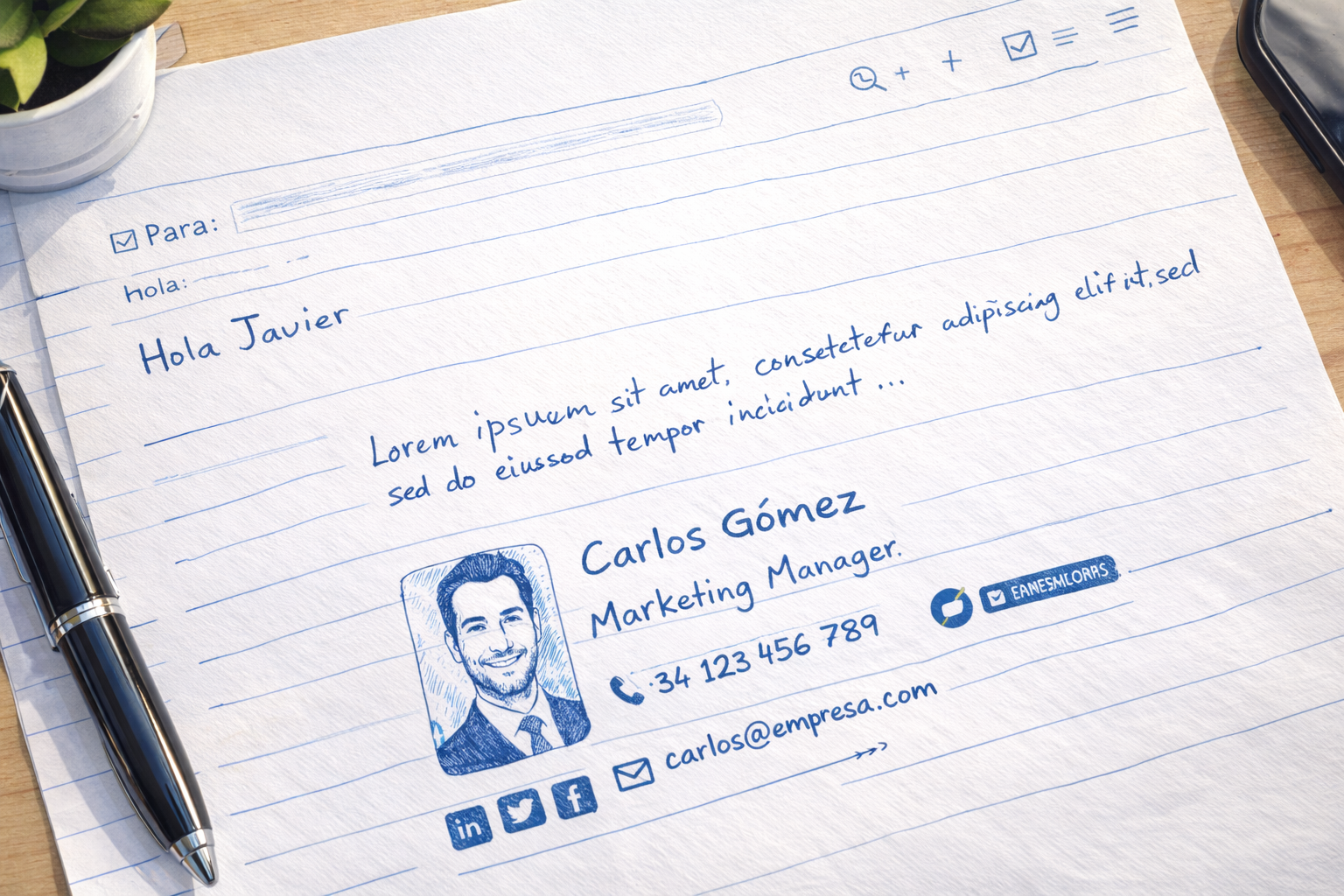
Content choices matter just as much as layout choices. Policies should also explain how campaign modules, local office information, and temporary exceptions are introduced and later removed. A signature becomes more persuasive when every line earns its place. If an item does not help identification, contact, compliance, or conversion, it is probably consuming space that could be used more effectively elsewhere. This is also where imagery needs discipline. A headshot, logo, or campaign banner should clarify identity and create recognition, but it should never slow loading, dominate the message, or create awkward empty blocks when images are blocked by the email client. Thoughtful restraint improves both aesthetics and performance.
Support employees with policy-aware workflows
Even the best template fails if employees cannot use it confidently. If the policy is going to be followed, users need plain-language instructions and a publishing flow that reinforces the rules automatically. Good enablement means a new hire should understand how to generate, install, and verify a signature in minutes, not after a string of internal tickets. The workflow needs to explain what can be edited, what is locked, and where to go for help if something looks wrong. Teams often underestimate this part because the template feels finished once the design is approved. In practice, the success of a signature program depends heavily on whether everyday users can reproduce the approved version without having to interpret unwritten rules.
Edge cases are the fastest way to expose whether a process is genuinely ready. Common edge cases include dual-language signatures, acquired brands, contractors using company email, and leaders who want a one-off design treatment. A mature setup anticipates those moments before launch and includes fallback guidance that is short enough to be followed under time pressure. That is why support copy matters: concise internal instructions, screenshots, and one escalation path prevent people from improvising fixes that create even more inconsistency. The goal is not to eliminate every exception. The goal is to make exceptions boring, predictable, and easy to recover from without weakening trust in the template itself.
Check that the policy survives in real production use
Quality assurance deserves its own slot in the rollout timeline because email signatures break in ways that static mockups never reveal. Governance is stronger when release checks confirm the policy is visible in practice rather than sitting as an unused document in an internal folder. Test messages should be sent to real inboxes, forwarded internally, viewed on different screen sizes, and opened with images blocked as well as enabled. That process reveals spacing problems, alignment shifts, logo distortion, CTA visibility issues, and legal text that becomes unreadable once the email client applies its own defaults. QA is not an admission that the design is fragile. It is the discipline that turns a promising layout into a dependable production asset.
That includes confirming locked fields display correctly on the email clients most used by the business, because a policy that cannot survive production rendering is not a real policy. The practical lesson is simple: if one client matters to your organization, it deserves its own acceptance criteria. Teams get into trouble when they validate only in the environment preferred by the person building the template. A healthier habit is to define a small but non-negotiable testing matrix and use the same one every time the signature changes. That habit shortens future reviews because people stop debating what good looks like; they already have a clear benchmark for passing or failing a release.
- List every locked field and every editable field in plain language.
- Document who approves structural, legal, and campaign changes.
- Review a sample of live signatures against the written policy after rollout.
Assign approvals without creating bottlenecks
Once the signature is live, governance becomes the difference between a polished system and a slowly decaying one. Good governance is specific about roles, approvals, review frequency, and exceptions, yet still short enough to be read in one sitting. The healthiest setup gives people enough flexibility to keep their own contact details current while protecting the structural elements that carry brand and legal risk. That balance keeps employees productive without opening the door to constant redesign from department to department. Governance is most effective when it feels ordinary: one owner, one review cadence, one change log, and a short path for campaign or compliance updates.
A practical owner model often gives marketing authority over design, operations authority over deployment, and legal authority over disclaimer changes or market-specific requirements. This is especially important when responsibilities span marketing, operations, customer success, and regional teams. If ownership is vague, updates stall until a problem becomes visible in customer emails. If ownership is explicit, improvements happen quietly and the signature evolves without drama. That is the standard worth aiming for: a signature program that supports day-to-day communication so smoothly that most employees barely think about it, while leadership still knows it can be updated quickly when the business changes.
Use policy reviews to reduce repeat exceptions
Measurement closes the loop and proves whether the signature is helping the business or just decorating it. Track how often off-brand signatures appear, how quickly approved changes reach all users, and whether exception requests are increasing or decreasing. The right review does not obsess over vanity data. It compares expected behavior with real behavior: are employees actually using the approved version, are recipients clicking the right CTA, are support teams seeing fewer setup problems, and are updates reaching every market without lag. When those signals are reviewed consistently, the signature becomes easier to defend internally because it is tied to outcomes, not just personal taste or brand preference.
Policy quality improves when recurring problems are folded back into the rules, forms, and admin options so teams do not repeat the same debates. A useful cadence is a monthly operating review with a deeper quarterly refresh. Monthly reviews catch fast-moving issues such as broken links, seasonal campaigns, or low adoption in a specific department. Quarterly reviews create space for bigger questions around layout, localization, device behavior, and whether the signature still reflects the company you are becoming. Iteration works best when it is deliberate. Random edits create noise; structured reviews create compounding quality.
- Number of off-policy signatures found in routine audits.
- Average time to approve and publish a policy-driven update.
- Frequency and type of exception requests coming from different departments.
Final takeaway
The best governance policy is not the one with the most clauses. It is the one that quietly shapes everyday behavior and makes consistency easier than improvisation. The central idea to keep is that a signature succeeds when it feels effortless to the sender and reassuring to the recipient. That combination comes from operational clarity more than visual novelty. A thoughtful system gives teams confidence because they know every message leaves the company looking aligned, credible, and ready for the next action.
If you are updating this part of your email experience now, start small but start with the full system in mind. Define the owner, simplify the template, test the environments that matter most, and document how changes will be reviewed. Those steps may look simple, yet together they create the durable advantage most teams are actually looking for: signatures that are easier to manage, nicer to read, and strong enough to support the brand every single day.
